A Complete Packet Capture Appliance
& Network Security Platform
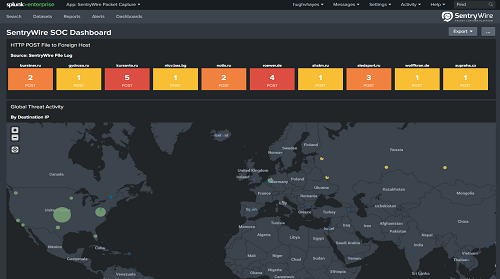
Whether you are trying to troubleshoot a networking issue or responding to a security incident, SentryWire can provide you full visibility into your network traffic, past & present.
Overview
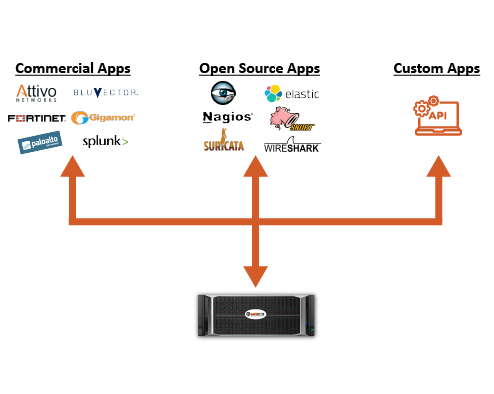
SentryWire is a Full Packet Capture Appliance and Network Security Platform that is based on a unique capture and storage architecture which breaks the performance, scalability and expense barriers of existing frameworks. SentryWire supports capture rates from 1Mbps to +1Tbps, while providing real-time filtering and allowing retention of network traffic for weeks, months and even years at price points that can be less than 50% the cost of other systems.
Imagine a Hadoop like architecture that is engineered to scale out compute and storage to provide the fastest search in the industry even in packet stores of 100PB's. The SentryWire system has high-speed packet recording with real-time analytics, visualization, and BPF-syntax filters. The system detects intrusions, minimizes damage caused by breaches and enables complete packet level analysis of any incident.
The SentryWire Packet Capture Platform allows an extended timeline of traffic to be recorded and analyzed at commodity prices using new or existing analytics. Why is it important to have an extended timeline of packet traffic stored? Because we know on average it takes 146 days to detect certain state sponsored intruders in a network and without a high fidelity recording of the network traffic enterprises cannot make a definitive determination of when intruders got in, how they got in or exactly what data was ex-filtrated.